Microsoft has recently announced that a new update is coming to Microsoft Edge browser. Among the several new features rolling in, sidebar search and history sync are two important. The one feature, which is currently the most talked about and promising addition, is the Password Monitor. This new feature will warn you if any password of yours has been stolen or compromised. The service was initiated to Insider members in June, 2020. Finally, it is making way to Public. The new version is Microsoft Edge 88.
Microsoft Edge allows its users to save their passwords in Edge and Edge remembers the saved passwords for the users. Like other web browsers, Microsoft Edge also has this Password manager capability. While doing this, Edge browser ensures that it does not have any information about those passwords. The Password Monitor will ensure that other than the user, no one else has access to his/her passwords.
Password Monitor is the result of a collaboration between Microsoft Research and a former research incubation group Cryptography and Privacy Research Group. It is an application of their ongoing research on homomorphic encryption. The teams have built on the Microsoft SEAL homomorphic encryption library to implement a new protocol to bring Password Monitor to our Edge users. According to Microsoft’s blog post:
“Homomorphic encryption is a relatively new cryptographic primitive that allows computing on encrypted data without decrypting the data first. For example, suppose we are given two ciphertexts, one encrypting 5 and the other encrypting 7. Normally, it does not make sense to “add” these ciphertexts together. However, if these ciphertexts are encrypted using homomorphic encryption, then there is a public operation that “adds” these ciphertexts and returns an encryption of 12, the sum of 5 and 7.
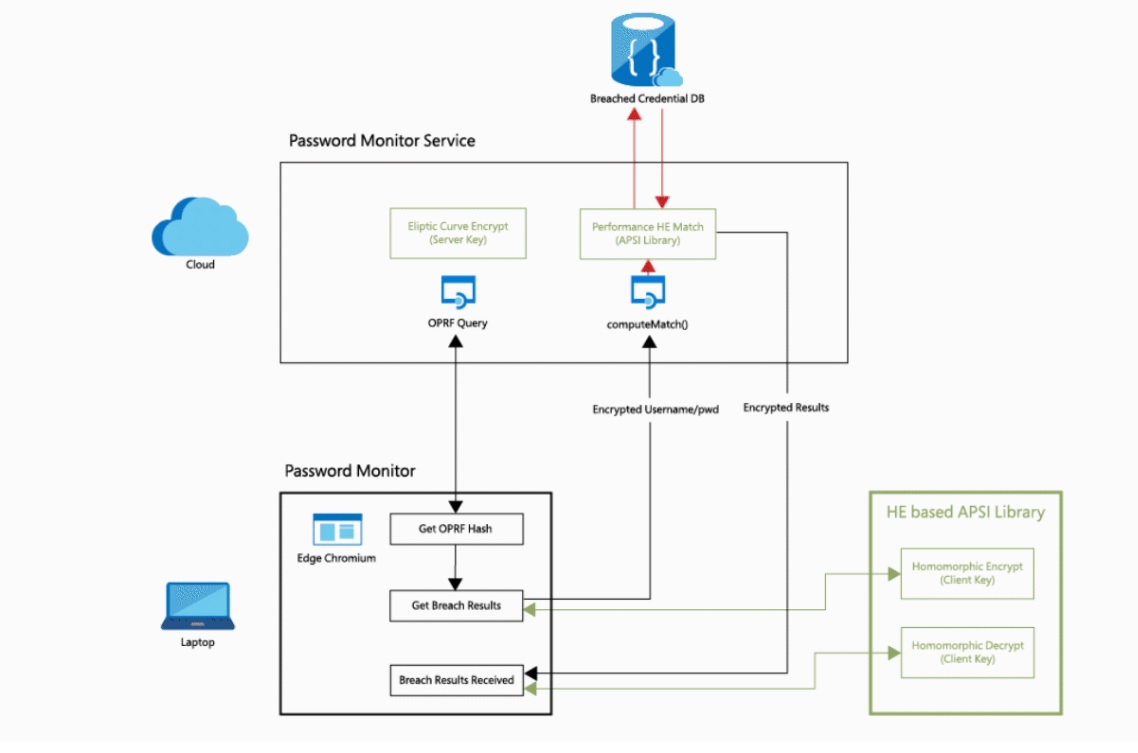
First, the client communicates with the server to obtain a hash H of the credential, where H denotes a hash function that only the server knows. This is possible using a cryptographic primitive known as an Oblivious Pseudo-Random Function (OPRF). Since only the server knows the hash function H, the client is prevented from performing an efficient dictionary attack on the server, a type of brute force attack that uses a large combination of possibilities to determine a password. The client then uses homomorphic encryption to encrypt H(k) and send the resulting ciphertext Enc(H(k)) to the server. The server then evaluates a matching function on the encrypted credential, obtaining a result (True or False) encrypted under the same client key. The matching function operation looks like this: computeMatch(Enc(k), D). The server forwards the encrypted result to the client, who decrypts it and obtains the result.
In the above framework, the main challenge is to minimize the complexity of the computeMatch function to obtain good performance when this function is evaluated on encrypted data. We utilized many optimizations to achieve performance that scales to users’ needs.“

