The following tutorial will help you to manage anti-malware boot start driver initialization policy in Windows 10. With the advent of highly efficient anti-malware applications, hackers have become more and more alert and have left no stone unturned while designing the latest versions of malwares. hackers are now creating rootkits that prevents the malwares from being detected by anti-malware software applications. So one of the toughest challenge is to detect malware that starts early in the boot cycle. Windows 8 and Windows 10 have introduced a very efficient and useful feature called Secure Boot which can protects the boot configuration by inducing an early launch anti-malware driver.
Anti-malware boot-start driver can return the following classifications for each boot-start driver:
Good: The driver has been signed and has not been tampered with.
Bad: The driver has been identified as malware. It is recommended that you do not allow known bad drivers to be initialized.
Bad, but required for boot: The driver has been identified as malware, but the computer cannot successfully boot without loading this driver.
Unknown: This driver has not been attested to by your malware detection application and has not been classified by the Early Launch Antimalware boot-start driver.
If you enable this policy setting you will be able to choose which boot-start drivers to initialize the next time the computer is started.
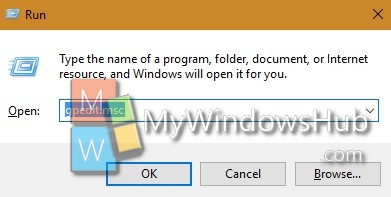
1. Press Win+R to open Run window.
2. Type gpedit.msc and hit Enter to open the Local Group policy Editor.
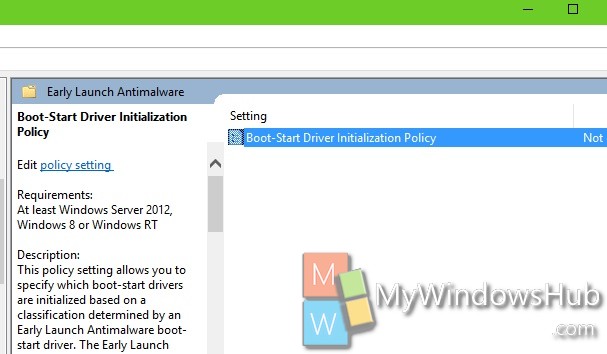
3. Now go to the following location Computer Configuration -> Administrative Templates -> System -> Early Launch Antimalware.
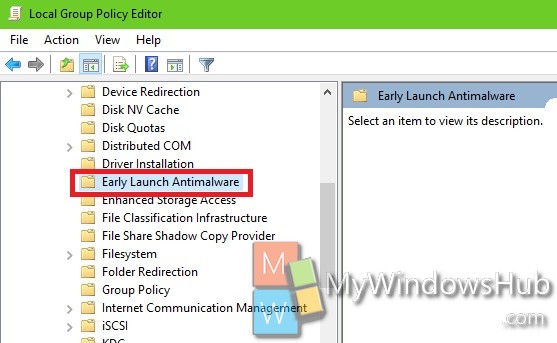
4. In the right panel, you will find the policy setting Boot Start Driver Initialization policy. Double tap on it to edit the policy.
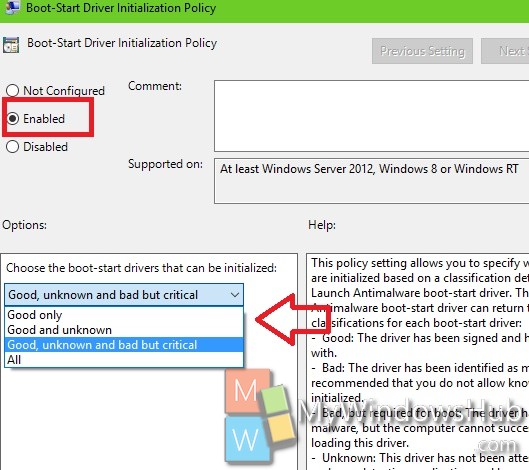
5. If you want to configure boot start driver initialization policy, then tap Enable. Now choose how the boot start drivers can be initialized. Choose among Good only, Good and unknown, Good, unknown and bad but critical. Go to Step 7.
6. If you want to disable the option, click on Disable.
7. Click OK and then Apply.
8. Close Local Group Policy Editor.