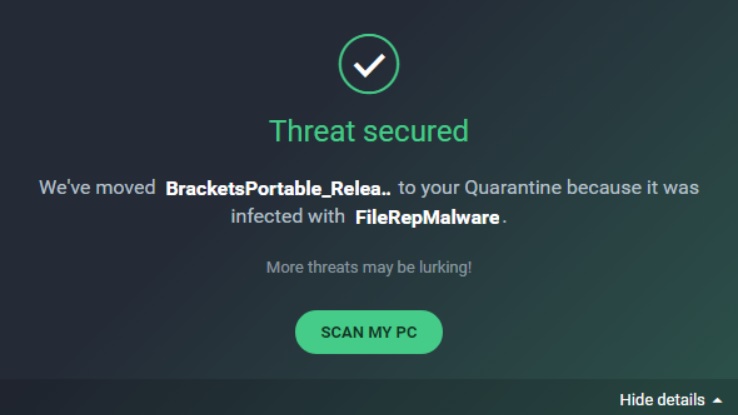
File Rep Malware is a simple tag used by 3rd party antivirus and assigned to a file. Users install 3rd party antivirus software with the free version of Windows to keep their system safe. The 3rd party products have their own criteria to deal with malware. In the case of File Rep Malware users are getting confused to handle. Whether it is dangerous or not, they should remove the file or not etc.
KMSPICO tool is the main victim of File Rep Malware tag which is used to activate Windows for free. Other than this tag is assigned by antivirus to any software or file which finds suspicious.
How File Rep Malware tag is assigned by antivirus?
The main criteria to assign the tag to any application that score of the application has to be low. Low score application means half downloaded file or have not been added to the antivirus clean list or does not have a proper signature from any trusted publisher or antivirus. The applications with low score are detected as a virus or malware in most of the cases and assigned to the File Rep Malware tag by antivirus.
There are various method to check an application is infected or not.
Virustotal
- If any file on your system is assigned with FileRepMalware by your antivirus use free online tool Virustotal to check the file is safe or not.
- Right click on the file on antivirus page and select the option which can find the location of the file.
- Open the Virustotal website from the location page. Click on chose file option to upload the suspicious file. Virustotal will show details of the safety status of the file.
Scanner
- You can use the portable malware scanner.
- Use another antivirus scanner for a second opinion
- Windows Defender boost-time scan is an offline scanner. This is the best option to detect the infected file. If you are using pirated windows and activate with the KMSPICO tool, then it’s the high risk to infect files of your system. So it’s highly recommended to use original OS and reduce the chance of virus attack.
You may use file Unlocker to unlock the FileRepMalware file. If it will be unlocked then delete it from the system.
Various ways of entering the malware to your system like:
- Using a pirated version of the operating system
- Fake update
- Access external file infected with malware.
- Infected e-mail attachment.
That’s all!

